The Security Event Horizon
There is no checklist substitute for adversarial thinking.
Is your company secure?
Someone on the board asks this at least once a year. Maybe the audit committee chair. Maybe the CEO after a headline. The question lands, and the answer comes back as a list. SOC 2 Type II. ISO 27001. PCI DSS if you take cards. MAS TRM if you operate in Singapore. NIS2 for Europe. A pen test report from a firm with a good name. A clean risk register. Cyber insurance from a carrier that did its homework.
The answer sounds like security, everyone treats it like security — regulators, auditors, insurers, trial lawyers — and your board expects the list. Your CFO signs off on the spend. Your General Counsel blesses the posture. So what’s the problem?
The question was the right question, but the list is the wrong answer.
Your CISO knows. The people responsible for your company’s security have been saying this for years. They were not in the room where the decisions were made.
The list confuses two things that were never the same, and that are now growing drastically apart. Compliance is a defensible paper trail of controls, of policies, of evidence that you’ve done what the system agrees is due diligence. But security is the live capacity to stop an adversary from doing the thing that ends your company.
It’s the difference between safety and security. Aviation checklists save lives. An airline pilot who fails to get down on the tarmac, inspect the plane and run their checklist would be grounded. The same with surgeons — you better hope your surgeon is running their checklist before they cut into you. Checklists protect against honest human error, against entropy, against physics. Checklists are magnificent in safety. The pilot runs the same list every time because the physics are the same every time. The surgeon’s checklist saves lives because the body on the table is not trying to outsmart the surgeon.
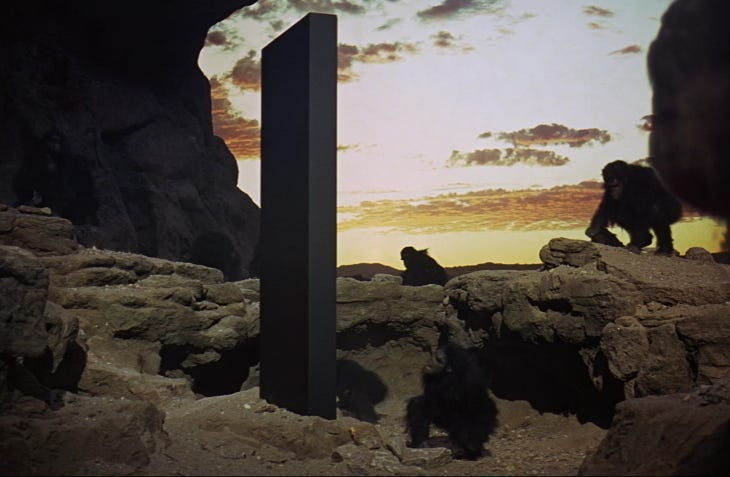
But there is no checklist substitute for adversarial thinking. This is true in every domain where an intelligent adversary is trying to beat you — in market competition, a court case, cybersecurity. War.
Checklists save lives. They don’t win wars.
For twenty years checklist compliance and cybersecurity defense — cyber war, if you’ll forgive the term — lived close enough together that treating them as the same thing gave roughly the right answer. They are now diverging. In a growing list of industries, they’ve come apart. Firms that haven’t noticed the gap will get eaten alive by predators on the cyber domain.
Checklists save lives. They don’t win wars.
That widening gap marks a point of no return. For the internet. For your business. For humanity.
Let’s call it the Security Event Horizon.
How did we get here?
Rewind. In 2013, hackers came through an HVAC vendor and walked out of Target with 40 million credit card numbers. Target ate about $200 million in costs. The CEO resigned. The stock recovered in two years.
That was the old world. The hit was real, large in absolute terms, small relative to the firm. The loss was bounded. The company survived. Target was compliant. They took cards. The compliance didn’t stop the breach. But the breach was old school: expensive, embarrassing, survivable. Target paid the bill and kept going. The conflation of compliance and security was wrong in theory and tolerable in practice.
In 2017, Russia’s GRU hacked MeDoc. What accountants in the Ukraine use. The Russians called the weapon NotPetya. Wiperware. Destructive. Sabotage. A software supply chain attack, infect all MeDoc users, destroy anything it touches.
A single laptop in a Maersk office in Odessa ran the software. Seven minutes later, Maersk — then moving roughly 20% of the world’s containers — lost 49,000 laptops and 7,000 servers across 130 countries. Eighty percent of the company’s IT, gone. For ten days the largest shipping firm on earth ran on paper, phone calls, and WhatsApp. The bill ran to $300 million.
Russia didn’t target Maersk. Maersk stood in the blast radius. No state declared war. No army crossed a border. A Russian weapon hit a Danish company on a Tuesday morning, and there were no border guards to stop them.
The Treaty of Westphalia is obsolete.
Maersk survived because one domain controller in Ghana happened to be offline during the attack, and because the firm was big enough to take the punch. A smaller carrier in the same blast radius might not have survived.
Maersk was a telegram from the future.
Shipping didn’t listen. The maritime industry read it as a bad Tuesday and went back to the frameworks. The International Maritime Organization adopted new regulations. BIMCO, ICS, and half a dozen other industry bodies published new guidelines. The US Coast Guard issued a cybersecurity strategy. Shipping responded to a military weapon with more paperwork. They thought checklists would help them win a war. Cyber incidents in the sector rose 900% between 2017 and 2020. By late 2024, one in three maritime professionals reported an infiltration in the prior twelve months.1 The frameworks were in place. The adversary didn’t care.
Shipping responded to a military weapon with more paperwork.
In 2025, North Koreans breached Bybit through a wallet vendor and took $1.5 billion in one transaction. An irreversible transaction. The exchange survived by raising emergency liquidity inside 72 hours. That’s the only reason it’s still around.
Bybit was compliant with every framework that applied. They took cards. But the compliance was irrelevant. Checklists don’t win wars.
The firm almost died.
Crypto is where this shift, this security event horizon, is most visible and most punishing. Military cybersecurity lives on the other side of the event horizon, and has since the beginning, but the losses are classified. OT and ICS/SCADA systems in water treatment, power grids, petroleum refineries, and manufacturing are also across, beyond the point of no return. The cyber risks are catastrophic and unbounded, waiting for an adversary with motive to destroy rather than steal. Medical devices are across it, but the loss shows up as patient harm, and the vast majority of devices currently in hospitals were manufactured before the FDA’s 2023 cybersecurity requirements. They lack the forensic logging to tell you whether they were hacked at all.
The losses in crypto are public, instant, and denominated in money that doesn’t come back. The visibility is why crypto is the case study. It is not the only sector that’s crossed over. Maersk wasn’t crypto. All those other industries aren’t crypto.
Here’s the problem: most senior leaders in those industries still think compliance is security.
It’s not.
The three-body problem
Your company is caught between three forces. In physics, there’s no stable solution when three bodies pull on each other. Two stars in a binary system? Clockwork. Three stars? Chaos.
Each is an adversary. Each pulls on governance, budget, and attention. None can be ignored. There is no stable orbit — but you can plan for the instability if you know the forces.
The regulator. Non-compliance produces consequences: fines, license revocation, audit findings, lost contracts, uninsurability. The signal is loud. The feedback loop is predictable. An alphabet soup of compliance regimes — SOC 2, ISO 27001, MAS TRM, NIS2, SOX, GBLA, GDPR, CCPA and more arriving every year. The solution is a bounded problem space: controls, audit artifacts, and policy documentation make the problem go away.
The market. Early movers capture share. Late movers die. A crypto exchange that takes two years to launch a product cedes it to the competitor who shipped in six months. An AI lab that slows its release cadence to improve weight security falls behind in capability benchmarks that determine funding and talent. A defense supplier that over-invests in security at the cost of delivery timelines loses the contract. The signal is loud. The feedback loop is predictable.
The cyber adversary. A state-backed or state-scale operator with the time, resources, and discipline to run multi-month intrusion campaigns, compromise third-party vendors, social-engineer employees, and maintain persistence through routine security reviews. The adversary can end your company in a single event. Or bleed it out slowly over time, like a cat playing with a mouse, one trade secret gone after another. The adversary sends no signal at all until the signal is a $1.5 billion transaction, or 49,000 dead laptops, or model weights on a server in Shenzhen.
The signal is silent. The feedback loop is unpredictable. Terminal.
Three forces. Two are loud. One is quiet. Good business orients toward noise.
This is not a failure of capitalism. This is capitalism working exactly as designed.
The market is an extraordinarily efficient noise-processing machine. It rewards what it can measure — revenue, growth, time to ship, market share — and punishes what it can measure too. Missed quarters. Lost deals. Slow launches. The entire system is built to process visible signals at speed.
Three forces. Two are loud. One is quiet. Good business orients toward noise.
Security against a silent adversary is the thing the noise-processing machine cannot see. There is no quarterly earnings line item for “breaches that didn’t happen.” There is no stock price bump for a red team exercise that found nothing because the defenses held. The market cannot reward the counterfactual. Capitalism handles security fine when the adversary is loud and the losses are bounded — when shoplifting is visible, when fraud shows up in the loss column, even when a cat burglar walks out of the building with a diamond. Capitalism handles the body of the distribution. The thing capitalism cannot handle is security against a fat-tailed, silent adversary whose feedback arrives as a single terminal event. The market cannot process that signal because the signal doesn’t exist until the firm doesn’t exist.
The regulator and the market both produce predictable, measurable consequences for failure. The adversary produces no consequence until the consequence is existential. In any system where resources are finite and signals compete, the loud signals win. Not because the decision-maker is stupid. Because the decision-maker is rational, and the information environment is asymmetric.
The predictable outcome: your company orients toward the regulator and the market — compliance and speed — and under-invests in the third force. The adversary. The quiet one. The third sun. The one that kills.
This is not a trilemma. A trilemma implies a choice among equals. Nobody is choosing. Your company is caught in a gravitational field where two of the three forces have immediate feedback and the third has delayed feedback, and the delay makes the third force invisible to the governance instruments you use to steer.
The gravitational dynamics choose for you, and they choose fast, compliant, and insecure every time. Overriding that default requires rewiring the governance — reporting lines, budget architecture, board information flow — not better judgment.
Three forces, one silent, pulling governance toward a threshold it can’t see and can’t come back from.
Here’s what to do about it.
What crypto built (and what it means for everyone else)
What changes when a company recognizes it’s got a three-body problem is not that the instability disappears. The company stops pretending it can solve the problem by spending more on compliance. The company orients deliberately toward the silent force: active, silent adversaries on the cyber domain.
The only way to do that is to acknowledge you are now at war. Not by choice. But when sovereign nations engage in coercive violence on the cyber domain against your firm to advance their geopolitical interests — there’s a common English word for that. And that’s war.
Whether you like it or not, foreign countries wage undeclared war on your private enterprise, your own government can’t protect you, and your choice is to confront the threat or let them cut you down.
The surviving crypto firms learned that lesson the hard way. They converged on three governance shifts. If your company has crossed the security event horizon — or will cross it — these are the three things you need to do. Not consider. Not evaluate. Do.
Every sector crossing the threshold will make these changes — deliberately and cheaply now, or reactively and expensively after the incident that forces the issue.
The templates to do this already exist. Banking built them after 2008 nearly destroyed the global financial system.
After the crisis, regulators forced structural changes that broke the old governance — where risk was managed by the same people generating revenue. A Chief Risk Officer with independent authority, reporting directly to the board risk committee, empowered to veto trades and block positions the revenue side wanted. Separate risk budgets — market risk, credit risk, operational risk, each with its own team, its own money, its own reporting, so the trading desk couldn’t cannibalize the risk budget to fund more trades. Board risk committees receiving risk reporting directly from the CRO, not filtered through the CEO or summarized in the CFO’s dashboard. Stress testing against tail scenarios — not “what’s our average expected loss” but “what kills us,” modelled annually, with the firm required to prove it survives.2
The crypto survivors arrived at the same three shifts. Here’s what they look like applied to cybersecurity.
Reporting line. The function responsible for defense against adversary-scale threats reports to the CEO and directly to the board, with authority to veto business decisions that create unmanageable exposure. The CISO in the new category is a de facto defense-only military leader3 — a Chief Cyber Risk Officer4 with a business mandate5, not a technical head reporting to the CIO with an advisory mandate. The business mandate includes authority to say no to products, partnerships, and vendor integrations that introduce existential exposure — regardless of the revenue they produce.
A CISO whose authority comes from a compliance framework cannot exercise this authority. The framework doesn’t grant it. A CISO whose authority comes from a CEO and the board can.
Budget structure. Adversary-specific defense is a distinct budget line, sized to the specific adversaries facing the company, protected from substitution by compliance spend, accountable on its own metrics. “The security budget” as a single line is how compliance displaces defense — within a single line, compliance wins every time.
Separating the two and forcing the board to see them separately is the only structural defense against the substitution.
Board agenda. The board receives named-adversary updates separate from compliance reporting. “Are we compliant with our regulatory regime?” and “What is our current exposure to our named adversary’s current TTPs?” are different questions with different answers. The board needs at least one director with the background to evaluate adversary-defense claims on their merits, not on the audit reports that accompany them. The SEC already requires listed companies to disclose cybersecurity expertise on the board.6 The requirement exists. Most boards fill it with a compliance background. The requirement should be filled with someone with a cyber defense background.7
CRO independence is the CISO reporting to the CEO and board. Separate risk budgets are the adversary-defense budget protected from compliance spend. Board risk committees are the named-adversary briefing. Stress testing is the red team exercise against a specific adversary’s kill chains. The structures are proven. The mapping is direct.
Banks didn’t build these templates proactively. They built them after catastrophe. The tuition was the global financial system. Crypto paid its own tuition. The question is whether the sectors crossing now will copy the homework or pay full price.
Banks built these templates after catastrophe.
A cautionary note from inside the community that should know better. SEAL — the Security Alliance — runs some of the best adversarial security work in crypto. Their SEAL 911 team handled over 1,800 support tickets in 2025 alone, coordinated over 125 war rooms during active incidents, and helped freeze tens of millions in stolen funds during the Bybit response.8 They operate a crypto-specific ISAC. They built a DPRK IT worker threat framework. The operational work is adversarial thinking in practice. They are very good at what they do.
SEAL also recently launched a certification framework. Modular certifications. Third-party audits. On-chain attestation badges. The fine print is honest: “Attestations do not indicate that a protocol is completely secure or free from issues.” No certification can make that claim. The badge answers the board’s question. The badge becomes the substitute. The floor becomes the ceiling.
The gravitational pull toward frameworks is that strong. Even the people who know will build them, because the system demands something auditable and the framework is the thing the system can audit. The pull is not ignorance. It is institutional gravity. It is the third body of the three-body problem. The question is whether the framework displaces the adversarial thinking or complements it. Most organizations, given a floor, stop climbing.
There is no checklist substitute for adversarial thinking. Not even a really good checklist, written by people who know.
Why this is happening now
If the three-body problem was always there, why is it only becoming lethal now? Because the third body was small for thirty years. Someone was suppressing it.9
Alfred Thayer Mahan worked this out in 1890 for a different domain, but the mechanism transfers.10 Mahan observed that maritime commerce depended on naval dominance of the trade routes. The Royal Navy policed the world’s sea lanes, suppressed piracy, enforced freedom of navigation, and denied those routes to competitors in conflict. British commerce flourished inside the space the policing produced. The commerce depended on the policing. The policing was invisible to the merchants whose ships sailed safely because it was there.
Everyone noticed the prosperity. Nobody noticed what made it possible.
The cyber domain ran the same way. The United States and its allies controlled the physical backbone — cables, routing, DNS, certificates, payment rails — through direct state action and through commercial intermediaries who had no choice but to comply.11 In 2013, Bruce Schneier wrote in The Atlantic that the NSA had commandeered the internet.12 The commercial platforms were not partners. They were conscripts. The East India Company model, updated for Silicon Valley.
The policing built on this commandeering was the foundation of the digital commerce boom. E-commerce (notice how now it’s just “commerce”?), cloud, SaaS, mobile payments, social platforms — all of it grew inside the space the hegemon’s policing kept low-friction enough to build on.
Everyone noticed the growth. Nobody noticed what made it possible.
Until the policing stopped. The architecture the hegemon built was the first vulnerability — and it was deliberate.
The internet was not designed to be secure. It was designed to be connected. No privacy by design. No confidentiality by design. No integrity verification by design. No availability guarantees by design. BGP — the protocol that routes the entire internet — has no native authentication. Countries have hijacked each other’s traffic. It’s not a vulnerability. It’s the specification.13
The hegemon made security worse on purpose.
The NSA spent the 1990s deliberately weakening commercial encryption so they could read it. “Collect it all. Know it all. Sniff it all.”14 When overt attempts to mandate government backdoors failed (the Clipper chip, 1993), the agency worked through standards bodies. NIST adopted Dual_EC_DRBG in 2007. Snowden documents later confirmed the NSA backdoored the algorithm. RSA built it into their widely deployed BSAFE library — after accepting a reported $10 million bribe from the agency to make it the default.15 A standard used globally by firms who had no idea they were using a backdoored algorithm.
The commons functioned because the hegemon policed it, not because the architecture secured it. The hegemon needed to read what it wanted to read, so confidentiality was a bug it never fixed. These choices left the commons wide open to the hegemon. They also left it wide open to anyone else who could operate at the same scale. For thirty years, only one party could.
That’s ending.
The hegemon’s capacity to police the commons is eroding. China, Russia, and the BRICS nations have built alternative infrastructure — cables, payment rails, routing — outside Western control.16 Dozens of capable nation-states now operate in the cyber domain, and the adversaries answer to no shared legal order. The US and Israel deployed Stuxnet against Iranian centrifuges — a cyberweapon that destroyed physical infrastructure in a sovereign nation without a declaration of war. China runs sustained espionage campaigns against commercial targets. North Korea runs theft operations against anyone holding digital cash.
“Hello, Pyongyang Police Department? I’d like to file a complaint.” See how far that conversation gets you.
The multipolar world is not coming. It’s here, and most people don’t know it yet. That has consequences for the cyber domain, the live-fire war zone where you and I now live and trade.
AI makes it worse. Capable open-source models put offensive capability in the hands of operators who previously lacked the skill, at a rate the defender economy is not matching. Defenders have to be right every time. Attackers only once. AI helps the offense more than the defense.
The domain that existed for thirty years was not the actual cyber domain. It was the cyber domain under hegemonic policing, which made the actual domain — borderless, stateless, adversary-permissive, designed insecure by the hegemon — look like a well-governed commons.
But Roman roads without Roman legions help only marauding invaders and brigands.
As the policing erodes, the actual domain reveals itself. The third body gains mass. The adversary force is no longer small enough to ignore.
You can insure against crime. You can insure against piracy. You cannot insure against war. The domain is producing war-scale events against firms with crime-scale governance.
Why making these changes is so hard
Compliance frameworks are not arbitrary. Regulators answered specific losses. Auditors answered regulators. Consultants answered auditors. Insurers answered loss patterns. Each framework is a snapshot of what the system agreed was due diligence on the day it froze.
Every general fights the last war.
PCI DSS arrived in December 2004, after credit card fraud exploded online and the card brands realized their separate security programs weren’t working. “Let’s build a framework,” they said. SOC 2 came in 2010 to address the cloud migration wave and the data breaches that came with it. “Let’s build a framework,” they said. ISO 27001 is a dinosaur from 1995, courtesy of the British government, which saw an absence of any security standards at all. “Let’s build a framework,” they said.
Ditto MAS TRM in Singapore. Ditto NIS2 in Europe.
“Let’s build a framework,” they said.
None of these frameworks are wrong about what they address. They work. A firm like Bybit that implements PCI DSS reduces the kinds of breaches PCI DSS imagines. PCI DSS does not imagine theft of $1.5 billion in fungible irreversible digital cash.17
The frameworks did something else, though. Something worse. They gave legal cover for negative externalities that hurt everyone.
Chemical companies have no profit-motive incentive to avoid toxic waste spills. So we regulate to force them to financially internalize those negative externalities.
And when data breaches were just personal information, who cares? Not the government. Not really. And not corporations — the market rewards fast to market. The data breaches hurt consumers. The commons. The punishment is usually a slap on the wrist. Cost of doing business. The profit stays with whoever shipped first.
Frameworks let the regulator point at something. They let firms show they’ve done something. They let insurers price something. Checklists don’t win wars. But they do let the bill for systemic insecurity get pushed into the future, because no single firm owns all of it, and for-profit means profit now, not some handwavy abstract highly-technical bad thing that may or may not happen in the future.
But that bill is coming due.
Until now, the consequences stayed bounded. For thirty years of digital transformation — human migration onto the cyber domain — the worst-case scenario was a data breach.
Those risks are no longer bounded. Now information is money. Information is the control plane of a water treatment plant that can poison a city. Information is the flight controls of a fighter jet. Information is the model weights that took a billion dollars to train. Edit someone’s blood type in their medical record and they die the next time they have surgery. The business has become information. Your firm. Damage the information and you damage the company. Steal the information and you take the company.
Different ball game. Same frameworks. That’s the problem.
The frameworks became a substitute for the only question that matters: are we safe from the adversary we actually face?
This is Goodhart’s Law applied to cybersecurity. The compliance metric became the target. The moment it became the target, it stopped measuring security.
Once the substitution set, the security people pushed back.18 They’ve been pushing back for more than a decade. Nobody with budget authority listened. The CISO ran the frameworks and was assumed to have answered the question. The CFO funded the program and was assumed to have funded security. The board got the dashboard and was assumed to have done oversight. The people who knew the list was wrong were not in the room where the decisions were made.
The question — are we secure? — kept getting asked. The list kept getting accepted as the answer. And the people who knew the list was wrong didn’t have the organizational authority to change it.
The compliance system has no sensor for its own irrelevance.
The auditor certifies you against the framework the auditor was hired to certify you against. Whether the framework matches your actual threat is not the auditor’s job. It’s not in the checklist. Nobody signs off on the fit between framework and reality.
Crypto got the future first. Not because crypto is special. Because crypto faced, from day one, an adversary no framework had ever imagined — a sovereign with unbounded time and sanctions to evade — going after a loss mechanism no framework was built to stop: theft of fungible, non-reversible digital cash. The DPRK doesn’t care about PCI DSS. The DPRK wants the money.19
Crypto spent a decade finding this out, one expensive heist at a time. By 2022, the survivors had internalized the split. Compliance was still required, still funded, still audited. It just wasn’t security anymore. Security was its own thing — its own budget, its own people, its own reporting line, its own accountability. The two cooperated. Neither stood in for the other. The CISO leads both.
Even knowing the split, making the structural change is brutal. The gravitational pull back toward compliance operates through channels the CISO can’t easily override.
That’s because not only is the third body silent, the risk it poses is impossible to quantify. The “green book” crowd wants to assign a probability to every threat and put a dollar figure on every risk.20 You cannot calculate probabilities without data, the cyber data gets stale in years, and insurance companies are actively refusing to underwrite the risk because they can’t model it. You cannot put a number on whether North Korea will decide your protocol is next. Cyber risk quantification is astrology with spreadsheets.21
Cyber Risk Quantification is astrology with spreadsheets.
If you can’t put a number on the threat, you can’t defend the budget. The budget process defaults to what it can measure. Rational CISOs and CFOs converge on the compliance set. CISOs know they’re scapegoats — they know the compliance set won’t stop the adversary that matters. They converge on it anyway. Not because they believe it’s the right set of controls. Because deviating is career-ending risk, and conforming is career-safe operational cost. The CISO who gets breached while running the standard frameworks keeps their job. Most of the time. The CISO who gets breached while running a non-standard adversary-first program gets personally charged by the SEC.22
The signal-strength asymmetry from the three-body problem translates directly into career incentives. A CISO who funds a red team exercise against a named adversary cannot point to a framework that required it. A CISO who funds the SOC 2 audit can point to the framework, the auditor, the insurer, and the board resolution. The first expenditure is better security. The second is better litigation posture. The second wins every budget cycle.
Everyone is covering their ass. No one is securing anything.
Compliance-saturated governance is structurally incapable of managing what it cannot measure. And the third body cannot be measured.
What does that look like in practice?23 At Drift, DPRK operatives spent six months manufacturing a friendship with the team, then used that access to drain $285 million in twelve minutes.24 Bybit was a different kill chain but the same adversary — supply chain compromise through a wallet vendor’s developer laptop, malicious code injected into the signing interface, $1.5 billion gone in a single transaction.25 KelpDAO, just last week, was simpler still: a single-DVN bridge configuration that should never have been deployed in production, $292 million.26
Everyone is covering their ass. No one is securing anything.
This pattern — compliance standing in for defense — is sector-independent. It displaced defense against DPRK theft in crypto exchanges between 2018 and 2024. It kept Maersk’s peers in shipping from restructuring their networks after NotPetya. No framework required it. It is now displacing defense against weight exfiltration in AI labs.
The compliance regimes differ. The career incentives are identical. The substitution is identical.
Compliance after you’ve crossed the event horizon is not merely insufficient. It’s negatively correlated with survival. The budget it consumes is budget adversary-specific defense doesn’t get. The authority it grants to Legal and GRC is authority the function responsible for the company-ending threat doesn’t have.
Compliance is negatively correlated with survival.
Compliance is not the villain. Compliance is yesterday’s answer to yesterday’s question, surviving by bureaucratic inertia and career rationality in organizations whose threat model has changed underneath them.
There’s a structural name for what the compliance-saturated organization becomes.
Fragile.
Not weak — fragile in the sense Nassim Taleb gave the term: a system that optimizes perfectly for known stressors and treats unknown stressors as zero. The framework’s completeness — its ability to address every adversary class it was built around — becomes the evidence the organization uses to conclude that nothing else needs addressing.
The organization is not negligent. It’s optimizing, successfully, for the wrong distribution.
It performs extremely well by every measurable metric. Right up until the day it doesn’t.
And the day it doesn’t is terminal.
Who crossed when, and who crosses next
Crypto crossed the threshold end-to-end between roughly 2016 and 2022. By Bybit’s $1.5 billion loss in February 2025, the survivors had traversed most of the governance evolution: CISO reporting lines elevated to CEO, adversary-specific budgets separated from compliance spend, board agendas treating named adversaries as standing items rather than generic risk line entries.
The firms that hadn’t traversed the evolution were the firms that didn’t survive. And even the survivors keep making mistakes — LayerZero allowing insecure single-DVN configuration as default, KelpDAO losing $292 million last week ago through exactly that configuration. The knowledge spreads unevenly. The three-body dynamic pulls governance back toward the default even after the lesson should have been learned.
Shipping and logistics got its warning shot in 2017 and didn’t heed it. Maersk absorbed NotPetya and went back to the frameworks. The next NotPetya will find the sector in roughly the same governance state as the last one.
The sectors crossing now, or poised to:
AI labs with frontier model weights. Crossed around 2023. Governance hasn’t acknowledged it. The adversary is named and state-scale: PRC-affiliated operators have publicly demonstrated sustained interest in model weight exfiltration and researcher-targeted intrusion. The loss mechanism is existential. A competitor state with current weights can produce a derivative model in months, collapsing the lead that justifies the lab’s valuation.
The compliance regime is still forming. When it arrives, it will be designed for AI safety rather than adversary defense. Labs building adversary-specific defense now will have the playbook the crypto survivors have. Labs waiting for AI safety regulation to tell them what to do will orient toward the two loud forces and ignore the silent one. The silent one is the one that ends them.
Defense contractors. The military-industrial complex has been targeted by nation-state adversaries for espionage and trade secrets for decades. This is not new. What crossed around 2022 is the governance threshold: the compliance regime (CMMC, NIST 800-171, DFARS) is now actively displacing adversary defense in exactly the pattern crypto lived through. The adversary is named: PRC, Russia, Iran, DPRK. The loss mechanism is existential — theft of controlled information disqualifies the supplier from future contracts. The frameworks are eating the budget the adversary defense needs.
Stablecoin payment processors. Crypto adjacent. Crossed around 2024 and accelerating. Same adversary and loss mechanism. These firms sit under banking-adjacent compliance regimes written for payment fraud and AML, not state-backed theft. Firms whose boards still treat this as a banking compliance problem will be among the first casualties.
Healthcare networks and medical device manufacturers. Across the threshold as of February 2024, when a ransomware attack on Change Healthcare — which processes roughly 60% of US prescription claims and handles medical billing for 900,000 physicians, 33,000 pharmacies, and 5,500 hospitals — took the company offline for months.27 In 2007, Vice President Dick Cheney’s cardiologist ordered the wireless function disabled on his implantable defibrillator. He was worried someone could hack it and kill the Vice President.28 That was nearly twenty years ago. The vast majority of medical devices in hospitals today still lack the security architecture to prevent it.
The sector has crossed. It sits at about the stage crypto was in 2020 — incident is public, scale is visible, governance hasn’t adjusted.
Pharmaceutical and biotech firms with high-value IP. Three to five years behind the leading edge. Loss mechanism is existential for single-product firms. Compliance regime designed around product safety and data integrity.
Manufacturing and industrial operators with integrated supply chains. Maersk is the template. Three to seven years behind.
Critical infrastructure operators with named nation-state adversaries. Water utilities, power grid, pipelines, ports. The adversary is named in every major threat intelligence report from the last five years. Five to ten years behind. The multipolar transition may accelerate it substantially.
The list will grow faster than anyone expects, because the conditions that produce the threshold are not independent of each other. The hegemonic policing is eroding. More state-scale adversaries operate in the domain, with fewer constraints. AI tooling lowers the cost of attack faster than it lowers the cost of defense.
The question for any given sector is not “are we safe.” The question is “how much time do we have before the shit hits the fan.” And the answer for most sectors is less than most people think.
The question
The question every senior leader should ask is not whether the organization is compliant. Compliance is table stakes. It will remain table stakes.
The question is whether the organization is battle ready.
Does your organization’s operational existence reside substantially in the cyber domain — in data, code, credentials, models, contracts, records, systems?
Is your governance structure built on the assumption that compliance with existing frameworks is a reliable proxy for security?
Do you assume your industry is years away from facing this kind of adversary?
For most organizations, the honest answers are yes, yes, and yes.
For most organizations, this combination is the exposure.
The risk.
War.
Companies that recognize this and close the governance gap before incidents force the issue will manage the instability the way the crypto survivors did. Companies that wait for incidents will pay for the education the way crypto paid, and the way Maersk almost paid, and the way the next Maersk is paying right now in a sector that hasn’t realized it’s the next Maersk.
Crypto is the future of enterprise security, unevenly distributed.
The distribution is accelerating.
The hegemony that policed the commons for thirty years is no longer doing the job at the scale the commons requires. The commons is reverting to what it always was underneath the policing — a live-fire war zone. Firms are finding out what that is, sector by sector, in the order determined by how hard they are to reach and how large the prize is.
The tail is getting fatter. The body of the distribution, which the compliance frameworks address, is getting less important to the expected value of total loss. This is not a cycle. It’s a one-way shift in the shape of the risk.
Crypto is the future of enterprise security, unevenly distributed.
I repeat: this is not a cycle. This is your business crossing the event horizon. There is no return ticket.
Governance built to ward off the regulator will fail to ward off sovereign nation-state armies.
If you’re still treating compliance as security, you’re not behind the curve. You’re on the wrong curve.
Your adversary is already inside. You just don’t know it yet.
J.M. Porup has spent a quarter century as a security practitioner, and a decade writing about it. He currently defends billions of dollars of fungible, non-reversible digital cash in his third CISO role in five years.
Maritime stat: DNV Cyber, Maritime Cyber Priority 2024/25, survey of 489 professionals, September-October 2024. 31% reported at least one infiltration in 12 months, vs 17% over five whole years in the 2023 study. Specific incidents: CMA CGM hit 2020, IMO itself hit 2020, DNV hit 2023, Port of Seattle hit 2024. IMO Resolution MSC.428(98) required cyber risk management with a compliance deadline of January 2021. Coast Guard mandatory cybersecurity plans not required until July 2027 — ten years after NotPetya. Industry bodies: BIMCO (Baltic and International Maritime Council), ICS (International Chamber of Shipping), INTERCARGO, INTERTANKO, and others.
The post-2008 governance reforms — Basel III, the Dodd-Frank Act, the OCC’s Heightened Standards — formalized the Three Lines of Defense model: first line (business), second line (risk management and compliance, structurally independent), third line (internal audit, independent of both). The CRO independence requirement, board risk committee mandate, and annual stress tests (CCAR and DFAST in the US) are now standard across systemically important financial institutions. These structures exist because the 2008 crisis proved that risk managed by the revenue function produces catastrophic failure.
SEC Final Rule, “Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure,” July 2023. Requires registrants to describe the board’s oversight of cybersecurity risk and to disclose whether any director has cybersecurity expertise.
Many civilian CISOs perform this job function to a high standard. Many ex-military, ex-spooks are uncreative, unable to anticipate their adversaries’ next move, and mired in their accustomed bureaucracy. Good CISOs can come from both backgrounds.
SEAL is a 501(c)(3) nonprofit with approximately $2 million in annual operating expenses and 28 volunteers on SEAL 911. See “Crypto exploit triage group SEAL sees uptick in tickets in 2025,” The Block, December 31, 2025. SEAL 2025 Financial Transparency Report at radar.securityalliance.org.
Bruce Schneier saw this in 2014: “The former governance model was largely a benign US dictatorship; the world believed the US was acting in the world’s best interests and looked the other way. That’s gone, that’s over, and it’s not coming back.” Schneier was talking about internet governance policy. This piece asks the question Schneier didn’t: what does the erosion of that dictatorship — arguably never benign — mean for the security governance of individual firms?
Alfred Thayer Mahan, The Influence of Sea Power Upon History, 1660-1783 (1890). Mahan’s argument that control of sea lanes determines commercial and military dominance became the intellectual foundation of US naval strategy and, by extension, the strategic logic that later applied to the cyber domain.
The US controlled: submarine cables (NSA UPSTREAM), root DNS and ICANN (Commerce Department authority until 2016), the dollar payment system (Treasury/SWIFT), and platform data (PRISM). The NSA programs UPSTREAM and PRISM were first reported by Glenn Greenwald and Ewen MacAskill, The Guardian, June 7, 2013. Lavabit shut down rather than comply with a National Security Letter, and the government punished the choice. See Glenn Greenwald, No Place to Hide (2014).
Bruce Schneier, “The US Government Has Betrayed the Internet. We Need to Take It Back,” The Atlantic, September 5, 2013. [We didn’t. Take it back, that is. —ed.]
On BGP hijacking: in 2008, Pakistan Telecom accidentally hijacked YouTube’s global traffic by announcing a more specific BGP route, taking the site offline worldwide. China Telecom has been documented rerouting US internet traffic through Chinese infrastructure on multiple occasions. On DNSSEC: specified in 1997, still not universally deployed nearly thirty years later. Email sender verification (DMARC, DKIM, SPF) arrived decades after the damage was done. The CIA triad — confidentiality, integrity, availability — was never part of the original architecture.
Attributed to NSA Director Keith Alexander. The phrase appeared in classified briefing slides published by The Guardian and The Washington Post in June-July 2013, based on documents provided by Edward Snowden. See also Greenwald, No Place to Hide, Chapter 2.
Joseph Menn, “Exclusive: Secret contract tied NSA and security industry pioneer,” Reuters, December 20, 2013.
China’s Peace cable system and Digital Silk Road create physical infrastructure outside Western policing. BRICS alternative payment rails (China’s CIPS, mBridge CBDC pilots) reduce dependence on SWIFT and the dollar system. The certificate authority system has been compromised repeatedly: DigiNotar failed in 2011 after Iranian-linked attackers used it to intercept dissidents’ Gmail; Symantec was removed from the trusted root list in 2018; CAs operate under every jurisdiction, and every jurisdiction can compel a CA to issue a certificate. US authority over ICANN ended in 2016.
Douglas W. Hubbard and Richard Seiersen, How to Measure Anything in Cybersecurity Risk, 2nd ed. (Wiley, 2023). The book claims to demonstrate “how to quantify uncertainty and shed light on how to measure seemingly intangible goals.” The insurance industry’s ongoing refusal to underwrite cyber risk at scale suggests the intangible goals remain intangible.
In October 2023, the SEC charged SolarWinds CISO Timothy Brown with fraud — the first time the SEC brought cybersecurity enforcement claims against an individual. Most claims were dismissed in July 2024; the case was dropped entirely in November 2025 under new SEC leadership. The chilling effect survived the case. Separately, Uber CISO Joe Sullivan was convicted in October 2022 for concealing a data breach from regulators. Two CISOs, two federal cases, one message: deviate from the standard and you carry the liability personally.
Drift Protocol, “An Attack Six Months In the Making,” April 2026. Attributed with medium-high confidence to UNC4736 (AppleJeus/Citrine Sleet/Golden Chollima), the same DPRK group behind the Radiant Capital hack in October 2024. The individuals who appeared at conferences in person were not North Korean nationals — DPRK actors deploy third-party intermediaries with complete employment histories and professional networks designed to withstand due diligence. See also The Hacker News, “$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation,” April 2026.
The Bybit attack was a multi-stage supply chain compromise. On February 4, 2025, attackers compromised a Safe{Wallet} developer’s macOS machine via a malicious Docker project. On February 19, they injected malicious JavaScript into Safe{Wallet}’s frontend, targeting Bybit specifically. On February 21, the manipulated UI showed signers a normal transaction while the underlying code redirected 401,347 ETH to attacker-controlled addresses. See Sygnia, “Investigation into the Bybit Hack” (2025); FBI attribution to TraderTraitor/Lazarus Group.
On April 18, 2026, attackers attributed to Lazarus Group exploited KelpDAO’s LayerZero bridge by compromising the RPC nodes used by a single Decentralized Verifier Network (DVN) — a 1-of-1 trust configuration. The attacker minted 116,500 unbacked rsETH (~$292 million), deposited it into Aave and other lending protocols, and borrowed ~$236 million in WETH. See Chainalysis, “Inside the KelpDAO Bridge Exploit,” April 2026.
American Hospital Association, “AHA Survey: Change Healthcare Cyberattack Impact on Hospitals and Health Systems,” 2024. 94% of hospitals reported financial impact. The attack exposed protected health information for an estimated 100 million individuals — the largest healthcare data breach in US history. The adversary was BlackCat/ALPHV, a commercial ransomware group that extracted a $22 million ransom. The compliance regime (HIPAA) was designed for data privacy, not adversary defense.
Cheney confirmed this on CBS’ 60 Minutes, October 2013. His cardiologist, Dr. Jonathan Reiner: “It seemed to me to be a bad idea for the vice president to have a device that maybe somebody on a rope line or in the next hotel room might be able to get into — hack into.” Cheney: “I was aware of the danger.”